For many organizations, the complex nature of modern IT systems can be mind-boggling. There is the constant challenge of managing internal service providers and multiple third-party vendors. Fortunately, service integration and management (SIAM) has emerged to bring sanity to an IT world plagued with chaos.
Welcome to your complete guide to the SIAM multi-supplier methodology.
Here, you’ll find insights that address the problems of a multi-sourcing ecosystem. We’ll explain how SIAM simplifies supplier management while keeping service quality high.
This guide will appeal to those seeking a broad set of ideas to help implement an effective SIAM governance model. It will also cater to those looking for ways to derive more value from their existing SIAM practices.
But we’re getting ahead of ourselves. Let’s first explore what Service Integration and Management really brings to the IT service delivery approach.
Key Takeaways
- SIAM is an approach to managing multiple service suppliers through a single service integrator function that coordinates collaboration and accountability across all providers.
- The service integrator role distinguishes SIAM from traditional ITSM frameworks by handling cross-provider governance, integration, and end-to-end service delivery.
- SIAM replaces ROI with Return on Value (ROV) and TCO with Total Cost of Consumption (TCC) to measure service delivery effectiveness beyond financial metrics alone.
- SIAM implementation follows four stages (Discovery and Strategy, Plan and Build, Implement, and Run and Improve) and is best initiated through incident, change, and problem management processes.
- SIAM and ITIL serve different purposes: ITIL provides best practices for service management, while SIAM adapts those practices for multi-supplier environments.
- Cross-platform integration tools that connect ITSM platforms like ServiceNow, Jira, Zendesk, Freshservice, and Azure DevOps are critical to operationalizing SIAM principles.
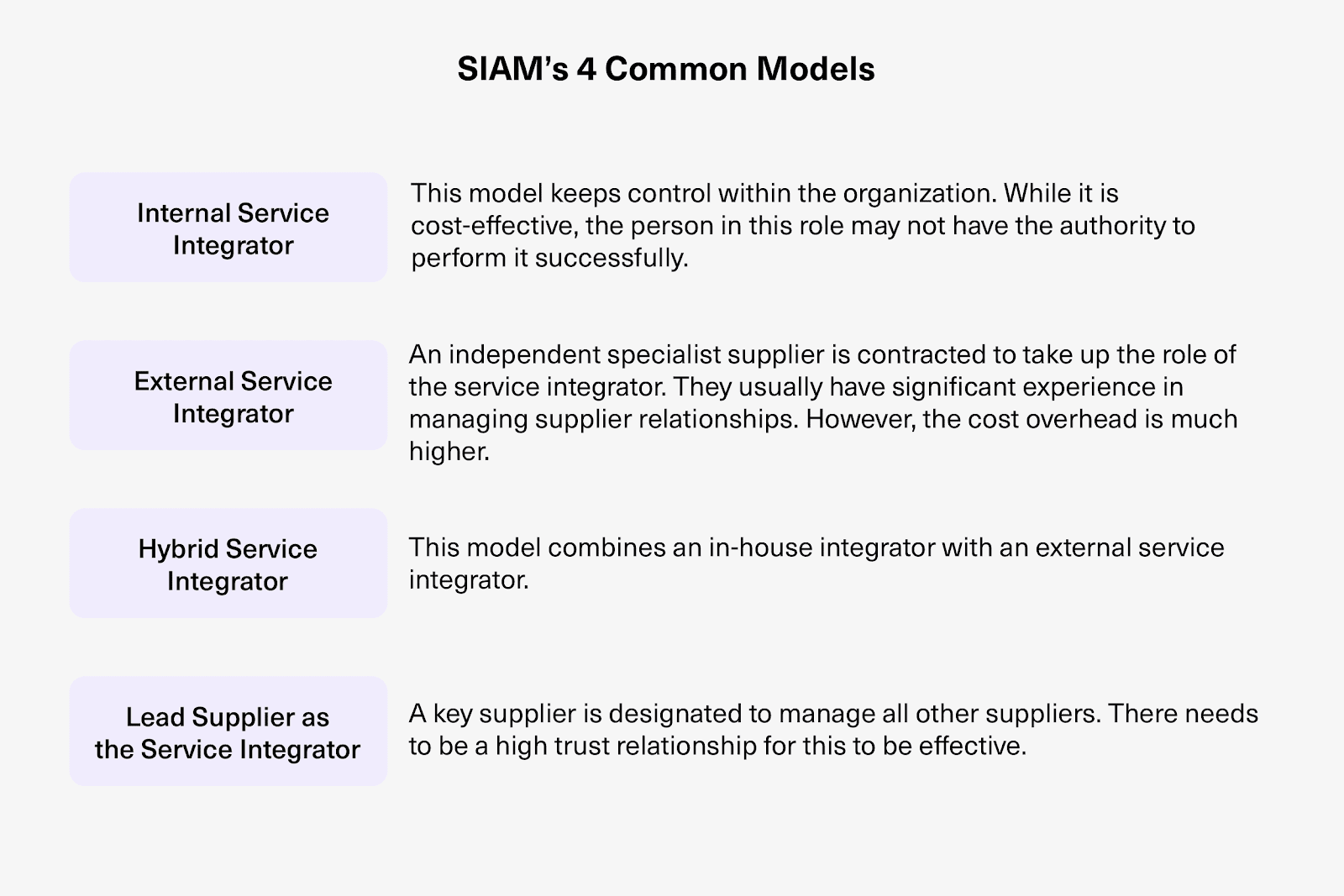
- Organizations can choose from four SIAM operational models (internally sourced, externally sourced, hybrid, and lead supplier) depending on their maturity, budget, and governance requirements.

What is SIAM?
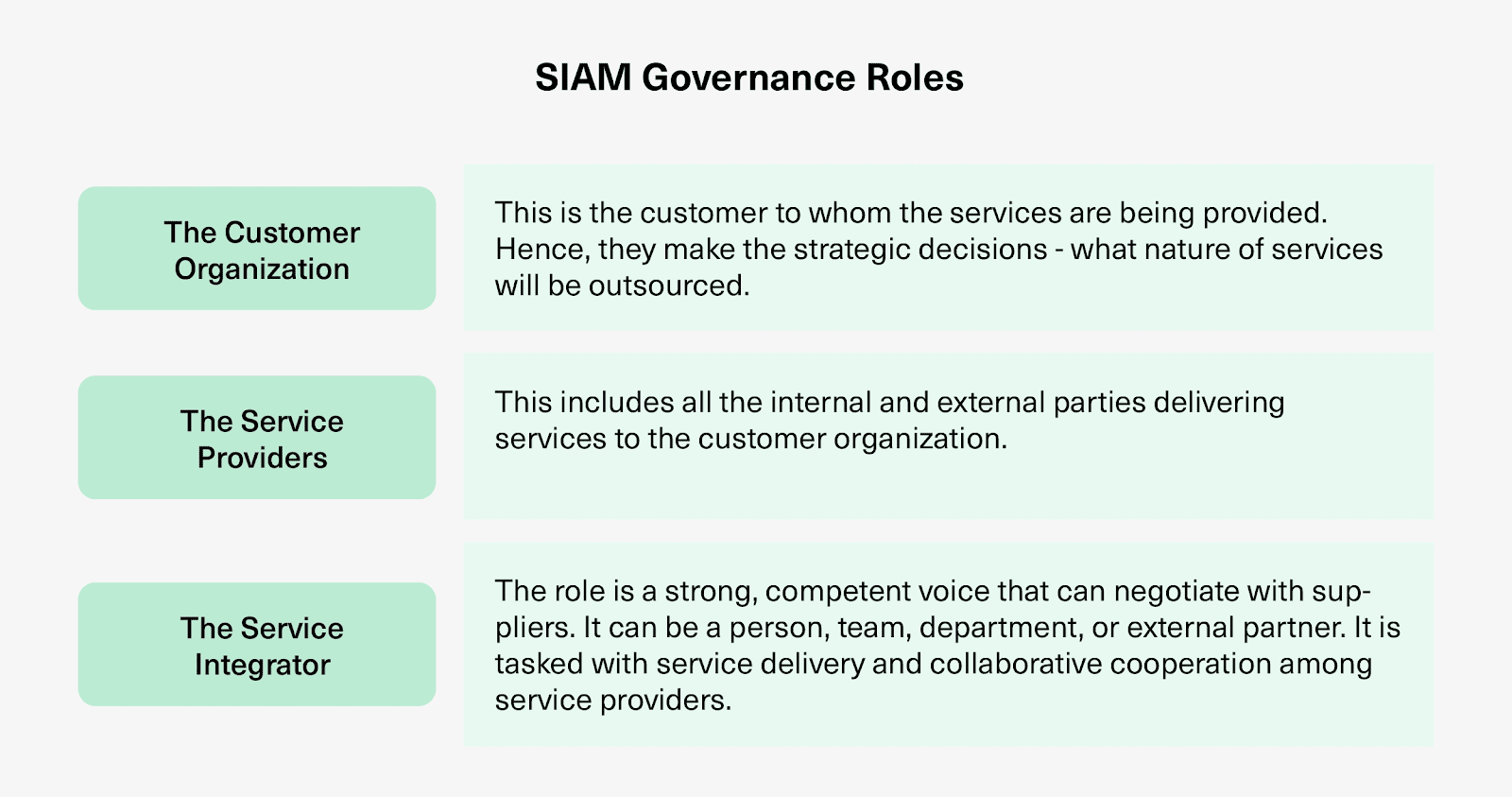
SIAM (Service Integration and Management) is an approach to managing multiple service suppliers by integrating them so they can collaborate and deliver consistent value to the customer. SIAM introduces the concept of a single, customer-facing logical entity known as the service integrator.

The service integrator is an independent function that handles the management and integration of multiple source partners. It takes on the complexity of multiple-provider service delivery by making solutions, technologies, and systems work together, with a focal point on technology integration.
In practical terms, think of an enterprise running ServiceNow for IT operations, Jira for development, Freshservice for a specific business unit’s help desk, and Salesforce for customer-facing service.
Without SIAM, each of those systems operates in a silo. The service integrator pulls them into a coordinated model where incidents, changes, and service requests flow across providers without manual handoffs or finger-pointing.
SIAM Key Concepts
SIAM as a methodology has been around for over a decade and is still evolving. However, it isn’t a process reference framework like ITIL and COBIT, or a standard like ISO/IEC 20000.
Even so, growing research into the field shows a clear distinction in purpose from its predecessors. SIAM smoothly combines related services from different providers into end-to-end services to meet business needs.
These are what separate SIAM from “old-fashioned” service management standards:
- Service integrator as a distinct function. Unlike traditional ITSM, where supplier management is a secondary concern, SIAM makes the integration of multiple providers the core focus. The service integrator coordinates across all providers, ensuring seamless delivery rather than leaving providers to figure it out on their own.
- Continuous improvement with cost optimization. SIAM’s service management system isn’t static. It targets ongoing improvement in service quality while sustainably reducing costs, balancing performance with value rather than chasing one at the expense of the other.
- Accountability for multi-provider integration. Service contracts under SIAM define expectations, manage risks, and realize benefits across all providers. This means no single provider can deflect responsibility when something breaks in the chain.
- Provider alignment with customer outcomes. SIAM shifts service providers away from individual performance goals toward delivering outcomes aligned with the customer’s expectations. A provider might hit every internal SLA and still fail the customer if the overall service experience is poor.
- Governance practices focused on business value. Management and governance under SIAM are designed to extract maximum value from service providers for the business, not just enforce compliance.
In addition, SIAM recognizes three governance levels within an organization (strategic, organizational, and tactical), each with distinct roles and responsibilities.
Apart from the service integrator, SIAM also introduces other key concepts into service management delivery:
- Key Performance Indicators (KPIs). SIAM ensures supplier performance through reliable metrics. Return on Value (ROV) becomes the ideal instrument because SIAM produces benefits that are both tangible and intangible. Total Cost of Consumption (TCC) replaces traditional ownership metrics because SIAM is inherently a consumer of services.
- Knowledge Management System. SIAM provides valuable guidance on best practices and proven IT service delivery techniques, creating a shared knowledge base that service providers can reference.
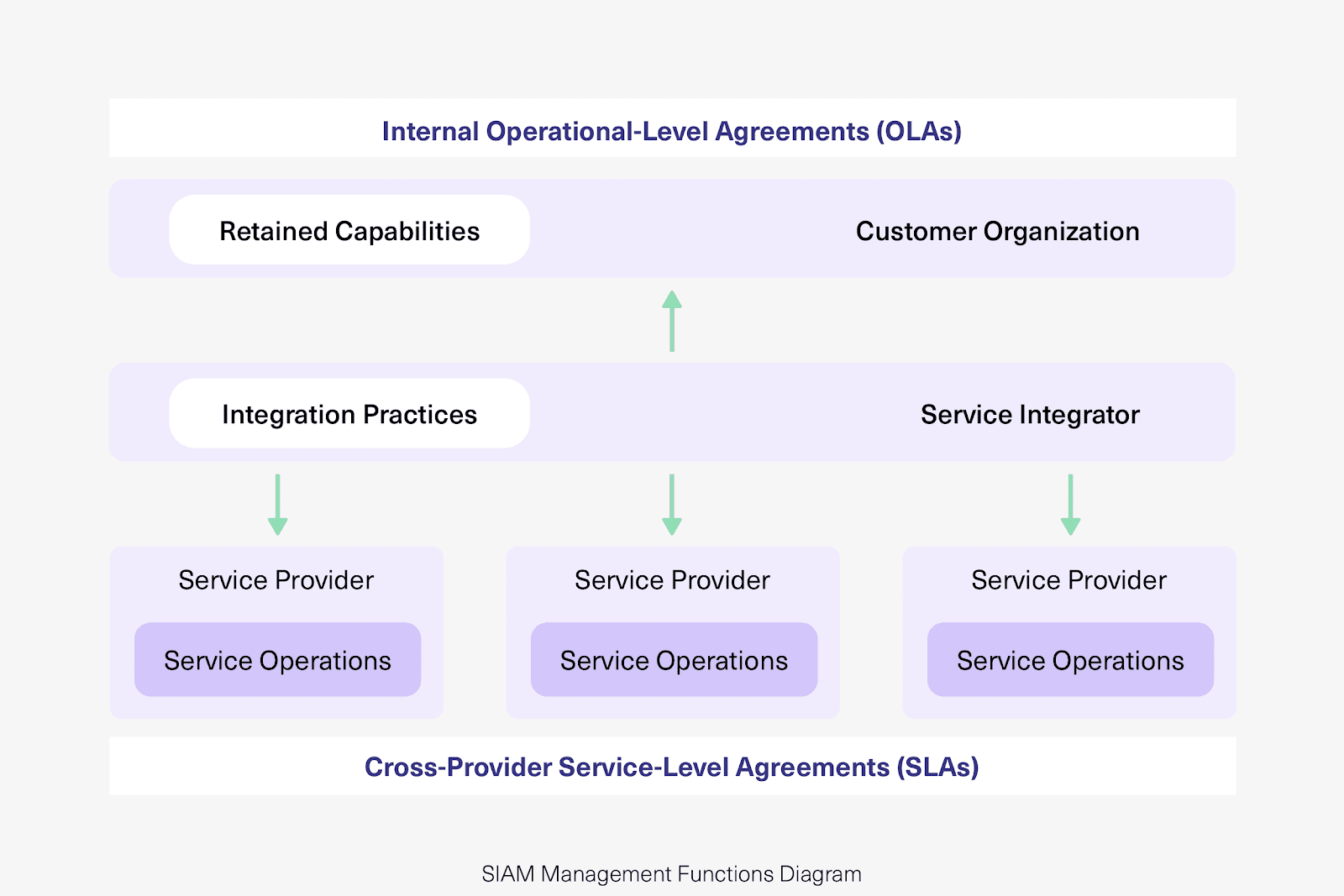
- Service Portfolio Management. SIAM provides supplier coordination, collaboration, integration, and interoperability through a governance framework backed by Service Level Agreement (SLA) contracts. All parties know their roles and responsibilities.
What SIAM is Not
SIAM is sometimes confused with vendor management or outsourcing strategy. It’s neither. Vendor management focuses on individual supplier relationships and contractual compliance.
The outsourcing strategy decides what to outsource and to whom. SIAM sits above both: it provides the governance and integration layer that makes multi-vendor delivery actually work as a cohesive service.
SIAM is also not a replacement for ITSM. It builds on ITSM processes and adapts them for environments where multiple providers need to collaborate rather than operate independently.

How does SIAM help an Organization?
Organizations have to do a lot to stay competitive. They consume services from a broad range of service providers in addition to developing their own delivery capabilities. SIAM is increasingly relevant because of the advantages it brings to multi-service delivery when implemented properly.
The Benefits of Service Integration and Management (SIAM)
- Increased accountability. SIAM creates end-to-end accountability for service delivery by making every provider aware of required outcomes and expectations. When an incident crosses provider boundaries, there’s a clear chain of responsibility rather than each provider pointing at the other.
- Optimized cost with improved value. Managing multiple operations and services is expensive. SIAM reduces that cost by eliminating duplicated effort across providers, streamlining processes, and ensuring the organization pays for consumed value rather than raw capacity.
- Effective risk management. By spreading services across multiple providers, SIAM enables organizations to avoid concentration risk. If one provider has an outage or fails to deliver, the SIAM framework provides fallback paths and clear escalation procedures. Tailor-made services from specialized providers further reduce the risk of a one-size-fits-all approach.
- Improved flexibility. Access to expertise from a wider array of service providers avoids costly vendor lock-in. If a provider isn’t delivering, the SIAM model makes it easier to substitute them without disrupting the entire service ecosystem.
- Increased expertise. SIAM allows organizations to assemble best-of-breed provider portfolios. Instead of settling for a single vendor’s capabilities across the board, you can pick the strongest provider for each service area.
- Improved governance and control. SIAM gives organizations the control they need over suppliers by providing clear governance structures, performance metrics, and escalation paths.
- Improved service quality. By integrating service delivery across providers and holding everyone to shared standards, SIAM enhances the overall quality of IT services reaching end-users.
The Role of SIAM in Changing IT Service Delivery Metrics
A common adage in business says, “If you can’t measure it, you can’t improve it.” This is relevant to IT services because they’re evolving from just being “cost centers” to things that deliver value.
Measuring the value of IT service delivery needs appropriate instruments that capture value. This creation of value is vital for suppliers in developing customer value models. Correspondingly, it enables customers to understand their own requirements and what satisfying those requirements is worth to them.
SIAM: Why ROV Overrides ROI
SIAM helps provide a supplier assessment framework that goes beyond price. The cheapest option doesn’t necessarily indicate you’re getting the best value. As Warren Buffett describes it, “Price is what you pay; value is what you get.”
Traditionally, businesses have used Return on Investment (ROI) as the measure of profitability. However, financial metrics don’t capture intangibles, which makes ROI an insufficient yardstick for SIAM.
Return on Value (ROV) provides a better way of articulating the value an IT initiative generates for business. It considers both tangible benefits (cost savings, efficiency gains) and intangible ones (improved collaboration, faster decision-making, reduced friction between teams).
For instance, when an integration between your ServiceNow instance and a service provider’s Jira environment eliminates four hours of daily manual ticket copying, the ROV captures not just the labor cost savings but also the reduction in errors, faster resolution times, and improved customer satisfaction.
SIAM: Why TCC Overrides TCO
Total Cost of Ownership (TCO) lets a business know what it’s spending on infrastructure. But it doesn’t specify what they’re really using. In a service-oriented model, this distinction is key.
IT services are meant to be consumed. SIAM is a consumer of services. Fixating on TCO for measuring SIAM is irrelevant because it tells you what you own, not what you use. TCC (Total Cost of Consumption) measures the cost per unit of consumption of IT services.
This is relevant because SIAM focuses on empowering organizations to co-create effective value through collaborative service delivery. A provider might own expensive infrastructure, but if the customer only consumes a fraction of its capacity, TCO paints a misleading picture of cost efficiency.
How does Service Integration and Management (SIAM) Work?
There is a tendency to define SIAM through the lens of process areas commonly associated with traditional IT service management (ITSM). But SIAM isn’t a process. It’s a methodology involving practices, processes, functions, roles, and structural elements.
SIAM in Practice
The central philosophy of SIAM that ultimately guides its practices is this: although you can outsource the provisioning of your organization’s IT services to third parties, you should never relinquish accountability for these services.
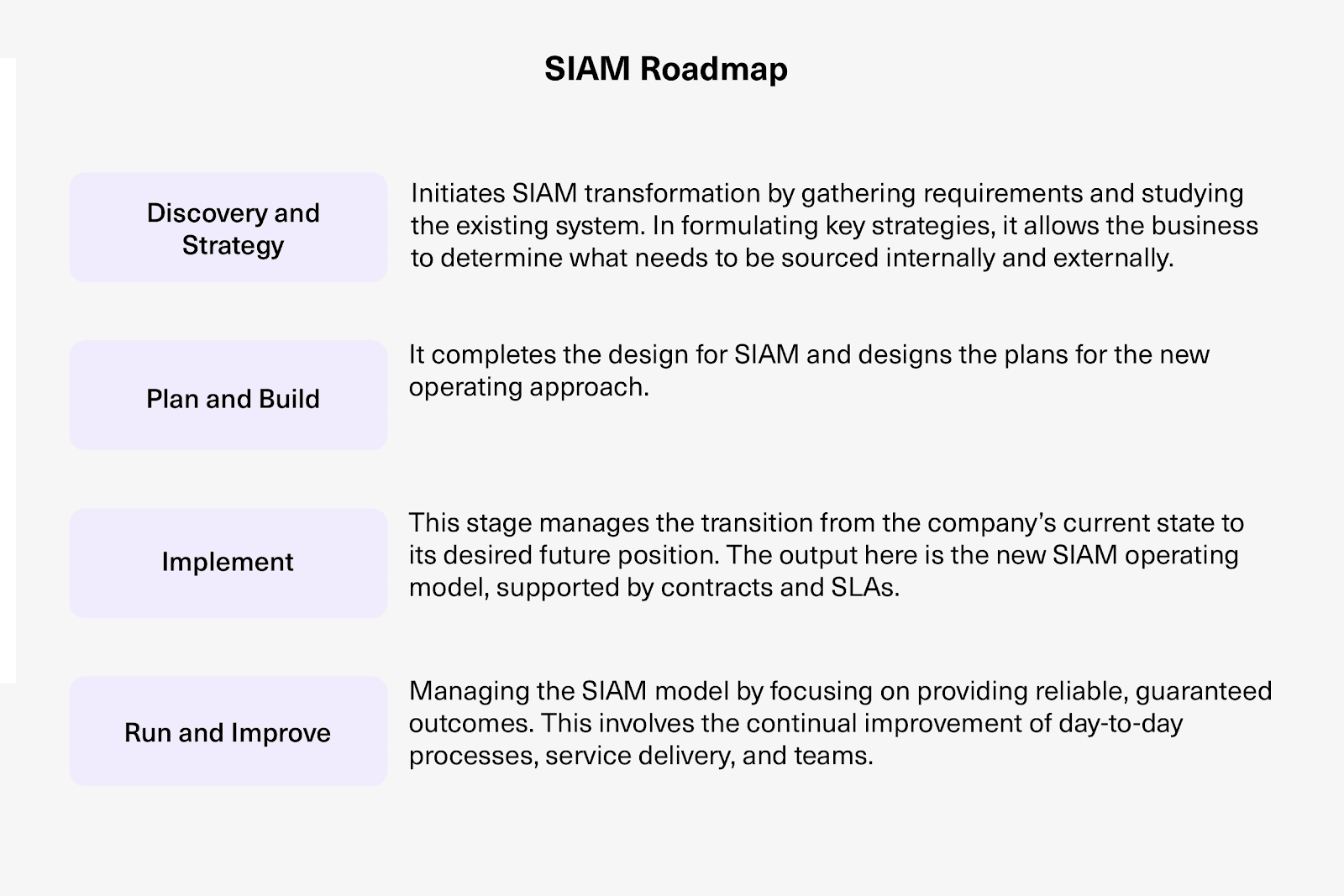
SIAM Foundation Body of Knowledge describes four stages that make up the SIAM roadmap:
Stage 1: Discovery and Strategy. This phase identifies the organization’s current state, defines the desired multi-supplier model, and establishes the business case for SIAM. It includes stakeholder alignment and high-level roadmap creation.
Stage 2: Plan and Build. Here, the SIAM model is designed in detail. This covers governance structures, process frameworks, tooling requirements, and contract structures for service providers. Integration requirements between provider systems are assessed at this stage, including which platforms need to exchange data and how.
Stage 3: Implement. The SIAM model goes live, typically starting with a pilot involving a subset of services and providers. Integrations between provider systems are activated, governance is enforced, and initial KPIs are tracked.
Stage 4: Run and Improve. SIAM enters steady-state operation with continuous improvement cycles. Performance data from integrated systems feeds governance decisions, and the model evolves as services mature.
Challenges in SIAM Implementation
- Process harmonization. Getting different suppliers to follow the same process is difficult. Each provider brings their own practices, escalation procedures, and reporting standards.
- Technology fragmentation. Providers use different platforms. One may run ServiceNow, another Jira, a third Freshservice, and a fourth Azure DevOps. Centralizing reporting and ticket flow across these platforms is time-intensive and complicated without the right integration tooling.
- Collaboration resistance. Parties may meet their contractual obligations but either can’t or won’t jointly invest the time to improve service delivery. This “letter of the contract” behavior undermines SIAM’s collaborative intent.
- Data visibility. Without real-time integration between provider systems, the service integrator lacks the unified view needed to manage end-to-end service delivery. Manual reporting and delayed updates create blind spots in governance.
When evaluating how to solve technology fragmentation, look for integration platforms that offer bidirectional synchronization, support a wide range of connectors (Jira, ServiceNow, Zendesk, Freshservice, Freshdesk, Salesforce, Azure DevOps, GitHub, Asana), and provide AI-assisted configuration to reduce setup complexity.
Platforms with ISO certification and a publicly accessible trust center provide the security assurance that SIAM governance requires. Exalate’s Trust Center is one example of this kind of transparency.
How to Get Started with SIAM
SIAM is a management methodology that draws on other management processes. There are 24 processes associated with it, listed in the SIAM Foundation Body of Knowledge by SCOPISM.
While all 24 processes have their place and purpose in a SIAM strategy, the best three to start with are:
- Incident management. The most immediately visible process is that incidents affect end-users directly and cross provider boundaries frequently. Starting here forces providers to establish shared escalation paths and communication workflows.
- Change management. Changes in one provider’s environment often ripple across others. Managing change across providers prevents uncoordinated modifications from disrupting service delivery.
- Problem management. Root causes often span multiple providers. Problem management in a SIAM context forces collaborative investigation rather than each provider closing the ticket on their side.
A SIAM Use Case: Incident Management
Let’s walk through a practical incident management example in the SIAM IT context.
Case: A customer uses Jira as their primary project tracker. They outsource IT management to two service providers, each running their own ServiceNow instance. Service Provider A monitors infrastructure and raises incidents like network outages, website downtimes, and system failures. Service Provider B handles critical customer-facing tickets.
Solution: When Provider A’s monitoring system raises an incident in ServiceNow, a corresponding work item is created automatically in Jira (Project A) with the necessary summary, description, attachments, and work notes. Similarly, when a critical customer ticket occurs in Provider B’s ServiceNow instance, a work item is created in Jira (Project B) for the dev team, with all relevant information attached.
Real-world application: The automation and integration between all these instances ensure appropriate conditions trigger work items in the right Jira projects. All required information is exchanged and acted upon in real time, with status updates flowing to stakeholders automatically. This eliminates the manual copy-paste cycle between systems, reduces mean time to resolution, and removes the finger-pointing that typically plagues multi-provider incident workflows. The service integrator gets a unified view of all incidents across providers without chasing individual reports.
Use Case: Cross-Provider Change Management
Case: An MSP managing a client’s cloud infrastructure (using Azure DevOps) needs to coordinate change windows with the client’s internal IT team (using Jira) and a third-party security provider (using ServiceNow). A major infrastructure change requires approval and coordination across all three parties.
Solution: When a change request is created in Azure DevOps, synced work items appear in both Jira and ServiceNow. Each provider reviews and approves the change within their own system. Status updates, risk assessments, and implementation notes sync bidirectionally, so all three parties see the same information without switching platforms.
Real-world application: Instead of a weekly change advisory board meeting where providers manually report status, the service integrator sees real-time change status across all providers. Conflicts between change windows are caught early because the integrated data flow surfaces scheduling overlaps automatically. The result is fewer failed changes, shorter implementation windows, and documented approval trails across all systems.
Use Case: Multi-Provider Problem Management with Shared Root Cause Analysis
Case: A government agency running Freshservice for internal IT support, ServiceNow for managed infrastructure, and Jira for development encounters recurring network latency issues. Each provider blames the others because they only see their own slice of the problem.
Solution: When a problem record is created in Freshservice, related records are synced to ServiceNow and Jira. Investigation notes, diagnostic data, and workaround information flow between all three platforms. When the root cause is identified in one provider’s system, the resolution propagates to all related records across platforms.
Real-world application: Instead of three separate investigations running in parallel (each concluding “the problem isn’t on our side”), the shared problem record forces collaborative investigation. The root cause is identified 60% faster because all diagnostic data is visible in a single context, regardless of which system generated it. The service integrator can track time-to-resolution across the full problem lifecycle, not just within individual provider boundaries.
The SIAM Operational Model
SIAM provides companies with a structure to manage vendors who supply IT services. It presents four common models. Organizations are free to choose whichever approach works best for them:
- Internally Sourced Service Integrator. The organization retains the service integrator role internally, managing all provider coordination with its own staff. This model provides maximum control but requires significant internal capability and tooling investment. Best for organizations with mature IT governance and dedicated integration teams.
- Externally Sourced Service Integrator. A third-party organization takes on the service integrator role. This model works well when the organization lacks the internal expertise or headcount to manage multi-provider coordination. It does introduce a dependency on the external integrator’s capabilities and responsiveness.
- Hybrid Service Integrator. The organization retains strategic oversight internally while delegating day-to-day integration operations to an external party. This provides a balance between control and capability, though it requires clear delineation of responsibilities to avoid overlap.
- Lead Supplier as Service Integrator. One of the existing service providers takes on the integrator role. This is cost-efficient since you’re leveraging existing relationships, but it creates a potential conflict of interest: the lead supplier is both a provider and the coordinator evaluating other providers’ performance.
Each model requires integration technology that connects provider platforms reliably. Regardless of the model chosen, the service integrator needs real-time data flow between systems to maintain governance and SLA compliance.
How SIAM Compares with Other ITSM Frameworks
IT Service Management (ITSM) touches on all lifecycle activities involving the creation, design, delivery, and support of IT services. However, ITSM and SIAM are often wrongly used interchangeably.
The noteworthy difference is supplier management. ITSM is aimed at managing IT services for an organization. SIAM builds on ITSM processes and helps adapt them for a multi-supplier environment.
SIAM vs. ITIL
ITIL is a set of practices that can be adopted for ITSM. SIAM is viewed as the next generation of ITIL. However, some argue that SIAM is merely using ITIL in a different way. This is partially true in the sense that SIAM is an adaptation of ITIL, but with a focus on multi-supplier delivery.
SIAM and ITIL work together to deliver services to an organization’s end users. They diverge in the sense that ITIL provides best practices for service definition activities. In contrast, SIAM assists organizations in sourcing the service from multiple vendors.
In summary, ITIL doesn’t “reflect multi-tenant sourcing models nor end-to-end service integration.” The service integrator role that SIAM supplies fills this void.
ITIL v3
ITIL v3 contains best practices for working with a single supplier. For the services provided, it suggests establishing delivery terms and conditions. Subsequently, you create operational-level agreements with internal business units and underlying contracts with external parties.
However, it says nothing about how you coordinate smartly with multiple suppliers. And in a world where most enterprises use 5-15 service providers for IT delivery, that’s a significant gap.
ITIL v4
ITIL v4 emerged in response to newer service management frameworks such as SIAM. It focuses on value creation and philosophies in the domains of service management. Examples such as DevOps, Agile methodologies, and development support processes readily come to mind.
ITIL v4 acknowledges the multi-provider reality more than v3 did, but it still doesn’t provide the depth of governance and integration guidance that SIAM offers for complex multi-supplier environments.
If you’re interested in learning more about ITIL 4 and the right choice for your service management approach, read this guide to ITIL 4 and service management.
Note: You might also be interested in this episode of Integration Talks, a podcast on everything integration, where Clair Agutter provides an overview of SIAM, its deployment, combining it with ITIL 4, and more.
SIAM vs. VeriSM
VeriSM is a more recent service management approach that targets the entire organization rather than just IT. While SIAM focuses specifically on integrating multiple service providers through a service integrator, VeriSM takes a broader view of how organizations deliver value through products and services, encompassing governance, people, and technology.
The two aren’t mutually exclusive. Organizations can use VeriSM’s Management Mesh concept at the organizational level while applying SIAM principles specifically to multi-provider IT service delivery.
SIAM vs. Lean IT and DevOps
Lean IT focuses on eliminating waste in IT service delivery. DevOps emphasizes breaking down silos between development and operations teams to accelerate delivery. Neither framework was designed for multi-supplier environments.
SIAM complements both. It provides the governance layer that coordinates Lean IT and DevOps practices across multiple providers. A service provider applying DevOps internally still needs SIAM principles when their delivery integrates with other providers’ workflows.
The Technology Foundation for SIAM: Integration Platforms
SIAM governance requires information to flow between provider systems in real time. Without this, the service integrator is managing from spreadsheets and weekly status calls rather than live data.
Integration platforms connect the ITSM tools used by different providers, enabling bidirectional synchronization of work items, incidents, changes, and problem records. The technology you choose to support SIAM directly impacts how effectively you can enforce governance and measure provider performance.
When evaluating integration platforms for a SIAM environment, focus on these criteria:
- Connector coverage. The platform should support the tools your providers actually use. Look for native connectors covering Jira Cloud, ServiceNow, Zendesk, Salesforce, Azure DevOps (Server and Service), Freshservice, Freshdesk, GitHub, and Asana. For niche or proprietary systems, REST API connector capabilities ensure you’re not locked out of connecting any platform in your ecosystem.
- Bidirectional synchronization. Data needs to flow both ways. If an incident is updated in ServiceNow, the corresponding work item in Jira should reflect that update automatically, and vice versa. One-directional sync creates information gaps that undermine SIAM governance.
- Independent control per side. Each provider in a SIAM ecosystem should control what data they send and receive through their own sync rules and field mappings. No provider should be able to override another’s configuration. This respects provider autonomy while enabling the data flow SIAM governance requires.
- AI-assisted configuration. Setting up integrations across multiple providers can be complex. AI-assisted configuration reduces this complexity by guiding setup decisions and generating initial sync rules. Exalate uses Aida, a scripting assistant that helps teams configure integrations faster and includes documentation assistance for ongoing management.
- Security and compliance. Integration platforms handle sensitive operational data crossing organizational boundaries. ISO 27001:2022 certification is the baseline. Look for vendors with a transparent security posture and publicly accessible compliance documentation.
- Scalability. SIAM environments grow as organizations add providers. The integration platform should handle increasing connection counts and data volumes without degradation.
Exalate is built for exactly this kind of multi-provider environment. It connects the major ITSM and project management platforms used across SIAM ecosystems, provides independent configuration control for each connected party, and uses AI-assisted configuration through Aida to reduce the setup burden. Each side of an integration defines its own sync rules without affecting the other party’s configuration.

How Exalate Fits into Your SIAM Model
An effective SIAM implementation entails cross-provider, cross-functional, and cross-process integration.
To reap the benefits of ROV in the SIAM context, it’s important to have a thorough understanding of how suppliers and providers can benefit from a cross-platform integration solution that promotes SIAM best practices.
However, the story is not limited to solution providers alone. It also involves getting customers on board by educating them on the advantages of choosing the correct service provider.
How SIAM Service Providers Can Use Exalate to Gain Competitive Advantage
Service providers and Managed Service Providers can offer integrations as part of their service. Such an effort solves the major hurdle of outsourced IT services: technology integration.
The ITSM toolsets used across the SIAM ecosystem are bound to be different. One provider runs ServiceNow, another Jira, a third Freshservice, and a fourth uses Azure DevOps. This creates a need for integration service providers like Exalate that allow cross-integration of ticket data and workflows from a single source of truth to multiple providers.
If integration is offered as a part of the service package, it insulates providers from the IT service chaos that occurs due to tool differences. With the right solution, the KPIs, SLAs, risks, security (backed by ISO certification), and other integration considerations are all handled through service contracts, setting the base for SIAM.
Exalate solves the inherent problem of coordination in SIAM by giving each service provider full and independent control over their side of the integration. Each provider defines what data they share and receive through their own sync configuration.
This overcomes the resistance service providers face while adopting SIAM, because they control their own configuration without worrying about how other providers might affect them.
With the right integration in place, service providers can turn it into their competitive advantage to win customers.
Effective ROV for the SIAM Customer
As a natural outcome of dealing with integrated service providers, customers no longer have to worry about how their technology stack will function with outsourced providers’ stacks.
They can expect enhanced service delivery with integrated processes and systems connected with their insourced or outsourced service providers. Using SIAM’s best practices, the TCC for SIAM customers will co-create value through collaborative service delivery.
Exalate: Your SIAM Sidekick
While SIAM keeps buzzing in the background and works on streamlining processes between service providers and customers, Exalate works tirelessly to ensure all the integration hassle is offloaded.
With integrated technologies, people, and processes, collaborations can happen in an automated and effective manner, turning SIAM into a reality.
If you’re considering how integration fits into your SIAM strategy, book a call to discuss your specific scenario with an integration engineer.

Frequently Asked Questions
What is Service Integration and Management (SIAM)?
SIAM is a management methodology for coordinating multiple service providers to deliver IT services as a cohesive, end-to-end experience. It introduces the service integrator role, an independent function that manages cross-provider governance, integration, and collaboration so that no single provider operates in isolation.
How is SIAM different from ITIL?
ITIL provides best practices for managing IT services, primarily designed for single-provider environments. SIAM builds on ITIL processes and adapts them for multi-supplier delivery. The key addition is the service integrator role, which coordinates across providers, something ITIL doesn’t address in depth.
What are the four SIAM operational models?
The four models are internally sourced (organization acts as service integrator), externally sourced (third party takes the integrator role), hybrid (strategic oversight stays internal while daily operations are outsourced), and lead supplier (one existing provider also serves as integrator). Each has tradeoffs around control, cost, and potential conflicts of interest.
What role does technology integration play in SIAM?
Technology integration is foundational to SIAM. Providers use different ITSM platforms, and without automated data synchronization between them, the service integrator can’t maintain a unified view of service delivery. Integration platforms that connect tools like ServiceNow, Jira, Zendesk, Freshservice, Azure DevOps, and Salesforce enable the real-time data flow that SIAM governance depends on.
How does Exalate support SIAM implementation?
Exalate connects the ITSM and project management platforms used across SIAM ecosystems, enabling bidirectional synchronization of work items, incidents, changes, and problem records. Each provider controls their own side of the integration independently. Aida, Exalate’s scripting assistant, provides documentation assistance and helps configure complex multi-provider integrations. Exalate supports Jira Cloud, ServiceNow, Zendesk, Salesforce, Azure DevOps (Server and Service), Freshservice, Freshdesk, GitHub, and Asana.
What security certifications should a SIAM integration platform have?
At a minimum, look for ISO certification, which confirms the vendor has a systematic information security management system. Integration platforms handle sensitive operational data crossing organizational boundaries, so security transparency matters. Vendors with a publicly accessible trust center provide the documentation needed for SIAM governance and compliance requirements.
What’s the best way to start implementing SIAM?
Start with three processes: incident management, change management, and problem management. These are the processes where multi-provider coordination breaks down most visibly. Establish shared escalation paths, integrate the ITSM tools providers use, and define clear KPIs before expanding SIAM governance to other process areas.
Can SIAM work for small and medium businesses?
Yes, though the model scales appropriately. Small businesses with two or three providers may not need a formal service integrator role but still benefit from SIAM principles: defined responsibilities, clear escalation paths, and integration between provider systems. The governance overhead of full SIAM implementation makes more sense as vendor complexity increases, typically around five or more active service providers.
Why does SIAM use Return on Value (ROV) instead of ROI?
ROI only captures financial returns and misses the intangible benefits that SIAM delivers, like improved collaboration, faster incident resolution, reduced friction between providers, and better end-user satisfaction. ROV accounts for both tangible and intangible outcomes, giving a more accurate picture of whether the SIAM investment is paying off.
How do you measure SIAM success?
SIAM success is measured through a combination of operational KPIs (mean time to resolution across providers, first-call resolution rates, change success rates) and value-based metrics (ROV, TCC, end-user satisfaction). The service integrator should track these across all providers rather than letting each provider self-report, which requires integrated data from the underlying ITSM platforms.
Recommended Reads:
- How to Build an Effective SIAM Operating Model
- B2B Integration: The Comprehensive Guide
- ITIL 4 and Service Management: The Right Choice for your Service Management Approach
- The Comprehensive Guide to iPaas (Integration as a Platform Service)
- The Definitive Guide to Cross-Company Integrations for IT Professionals
- ServiceNow Integrations: Integrate ServiceNow and Other Systems Bidirectionally
- Zendesk Integrations: Streamline Teams Working in Zendesk and other Tools
- Salesforce Integrations: Integrate Salesforce and other Tools
- Jira Integrations: Integrate Jira and Other Systems Bidirectionally